AWS configuration audits are a foundational mechanism for assessing cloud security posture, compliance alignment, and operational maturity. Across diverse client environments, these audits consistently demonstrate that most cloud risks do not arise from unknown zero-day vulnerabilities, but rather from well-documented misconfigurations that persist over time. Beyond identifying technical control gaps, configuration audits provide deep insight into the operational behaviors, governance models, and ownership structures that ultimately shape cloud security outcomes.
This article synthesizes recurring themes and systemic gaps observed across multiple AWS configuration audits conducted in varied enterprise environments.
1. Identity and Access Management Remains the Primary Risk Concentration:
IAM misconfigurations continue to represent the most prevalent and high-impact category of findings. Common patterns include:
- Overly permissive IAM policies, including widespread *:* usage
- Long-lived IAM users and access keys without rotation
- Inconsistent preference for IAM roles over static user credentials
- Absence of multi-factor authentication (MFA) for privileged identities
In many environments, access controls are optimized for speed and operational convenience rather than least privilege enforcement or long-term scalability. As a result, misconfigured IAM becomes a force multiplier for credential compromise and privilege escalation.
2. Network Exposure Is Frequently Underestimated:
Network-related misconfigurations remain common, particularly in rapidly evolving or decentralized environments. Observed gaps include:
- Security groups with overly permissive inbound rules
- Public-facing resources lacking strict ingress restrictions
- Inconsistent or ineffective use of Network ACLs (NACLs)
- Absence of an organization-wide baseline enforcing IMDSv2
Network security is often approached as a static, one-time configuration rather than a continuously managed control domain. Over time, incremental changes expand exposure surfaces, increasing the probability of lateral movement and escalation during security incidents.
3. Logging and Monitoring Are Enabled but Not Operationalized:
Logging and monitoring are frequently treated as compliance artifacts rather than active detection mechanisms. Recurring findings include:
- Monitoring not implemented for security events, resource changes, or unauthorised activity
- Lack of baseline enforcement for VPC flow logs and object-level logging
- CloudWatch alarms absent or not configured for security-relevant events
While logging may be technically enabled, it is often not integrated into an operational detection workflow. Without defined alerting thresholds, escalation paths, and ownership, visibility gaps persist despite the presence of logging infrastructure.
4. Encryption and Data Protection Controls Are Unevenly Enforced:
Although AWS services broadly support encryption, enforcement is inconsistent across environments. Common observations:
- Encryption enabled for select services but not uniformly across workloads
- Customer-managed keys not leveraged where regulatory or internal policy requires them
- Inconsistent key rotation and lifecycle management practices
This uneven application of encryption standards creates fragmentation in data protection posture, complicating compliance validation and increasing exposure in the event of compromise.
5. S3 and RDS Security Hardening Is Inconsistent:
Storage and database services are widely deployed, yet their security configurations frequently vary across accounts and regions. Observed behaviors include:
- S3 buckets permitting HTTP requests
- Public Access Block and MFA Delete are not consistently enforced
- RDS instances exposed to broad network CIDR ranges
- RDS instances lacking encryption at rest or in transit
Misconfigurations in storage and database services significantly elevate the risk of data exposure, regulatory non-compliance, and inadequate recovery posture during incident response.
6. Region-Based Configuration Drift Introduces Governance Blind Spots:
Regional governance is often underestimated during configuration audits. Common patterns include:
- Security controls enforced only in primary regions
- Inconsistent baseline configurations across regions
- Logging, monitoring, and AWS Config coverage are absent in newly enabled regions
- Lack of governance mechanisms restricting or approving region activation
Workloads deployed in secondary or newly activated regions frequently operate outside standardized guardrails, creating unmanaged attack surfaces and compliance blind spots.
7. EFS Adoption Was Not Observed:
Interestingly, Amazon Elastic File System (EFS) was not utilized in any of the audited environments. In most cases:
- Teams defaulted to S3 or EBS-backed storage models
- EFS was not enabled at the account level
While not a risk finding, this observation highlights architectural preferences and potential gaps in service evaluation or workload optimization.
Distribution of AWS Configuration Audit Findings
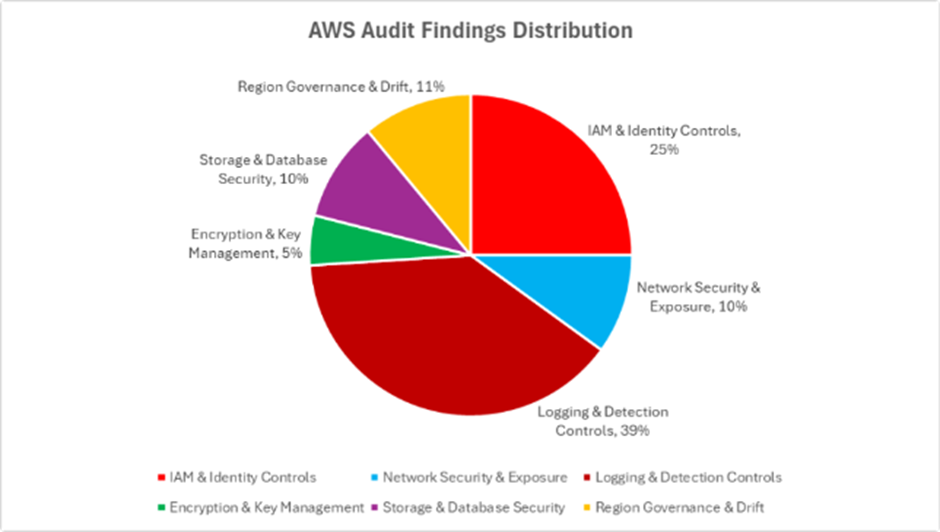
The distribution of findings reveals that Logging and Detection Controls (39%) constitute the largest concentration of gaps, underscoring persistent challenges in visibility and monitoring maturity. IAM and Identity Controls (25%) represent the second-largest category, reinforcing the systemic risk associated with privilege governance and access design.
Network exposure, storage, database hardening, and regional governance collectively account for a significant proportion of findings. Although encryption and key management issues appear less frequently in volume, they remain high impact from both a compliance and data protection standpoint.
Overall, the distribution indicates that cloud risk is less a function of missing capabilities and more a reflection of inconsistent operational enforcement, fragmented governance, and insufficient monitoring across foundational controls.
Conclusion
AWS configuration audits consistently demonstrate that cloud security risk is not driven by the absence of security services, but by how those services are configured, governed, and validated over time. Recurring patterns across client environments include identity mismanagement, expanding network exposure, logging gaps, uneven encryption enforcement, and region-based configuration drift, often influenced by rapid delivery cycles and decentralized ownership models.
These findings reinforce that configuration security is not a one-time implementation effort, but rather a continuous operational discipline that requires defined ownership, standardized baselines, and ongoing validation. Even well-architected environments accumulate risk over time in the absence of governance rigor and enforcement mechanisms.
When configuration audits are treated as a continuous feedback loop rather than a periodic compliance exercise, organizations materially improve their ability to reduce exposure, enhance detection capabilities, and sustain a resilient cloud security posture.