PCI DSS
Most payment breaches result from weak cardholder data security controls.
Strengthen payment data security and achieve PCI DSS compliance with Accorian’s expert-led assessment and advisory services. We help organizations identify security gaps across systems that store, process, or transmit cardholder data, aligning controls with PCI DSS requirements to reduce risk and protect sensitive payment information.
What is PCI DSS?
Payment Card Industry Data Security Standards (PCI DSS) are rules set by the PCI Security Standard Council (PCI SSC) about how things should be done. This rule applies to everyone who stores, processes, or sends data about cardholders. PCI DSS has become a global standard managed and updated by the PCI SSC to ensure proper implementation and compliance. The precise requirements may differ depending on how involved an entity is in the payment process.

Accorian is PCI QSA
Our certified QSAs play a pivotal role in safeguarding cardholder data. Through on-site and remote assessments of security controls, we not only evaluate compliance but also provide valuable insights and recommendations for improvement. Additionally, we support the development and implementation of essential security policies and procedures.

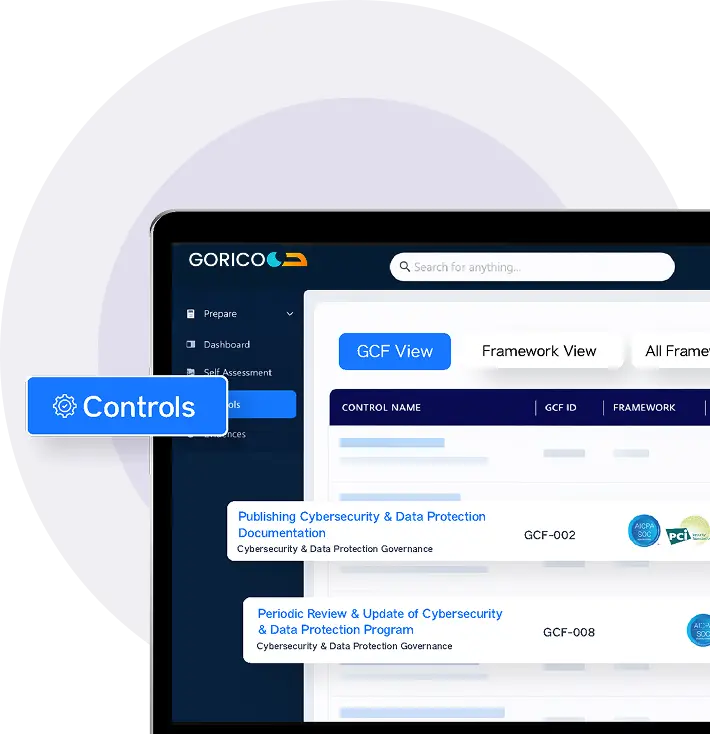
How GORICO Accelerates Your PCI DSS Journey
GORICO, with its AI-enabled capabilities, streamlines the PCI DSS process by centralizing control documentation, automating evidence collection, and enabling structured workflows across stakeholders while reducing manual effort, accelerating reporting, and strengthening overall control governance, making PCI DSS examinations more predictable and efficient.
Smarter GRC. Faster Outcomes.
FRAMEWORKS
Evidence Reusability
INTEGRATIONS
Hours SAVED
The Accorian Approach
- Define and finalize the optimum scope
- Define the flow of credit card data
- Identify the systems, processes, and controls relevant to your organization
- Finalize the scope
- Understand the current state of your PCI compliance
- Conduct a thorough assessment of the current security practices, policies, and controls against the requirements of the PCI framework
- Identify current gaps and implement the security measures to ensure compliance
- Provide a prioritized remediation plan
- Implement corrective measures by your team to resolve the identified errors/deficiencies and improve the overall security posture of the client
- Remediate advisory via calls to aid in addressing queries
- Detect the final set of gaps that need improvement before the final audit
- Ensure the organisation is ready for the formal audit and attestation conducted by PCI DSS QSA
- PCI DSS QSA conducts the final audit and provides the report of the PCI DSS
What Data Does PCI DSS Impact?
Cardholder Data includes information required for transaction processing, while Sensitive Authentication Data refers to sensitive details used for authentication, such as PINs or CVVs. While Cardholder Data can be stored if encrypted, Sensitive Authentication Data, on the other hand, must never be stored after authorization to effectively minimize the risk of fraud.
Card Holder Data & Sensitive Authentication Data
- Primary Account Number (PAN)
- Cardholder Name
- Expiration Date
- Service Code
Sensitive Authentication Data Includes
- Full Track Data
- Card Verification Code
- PINs/PIN Blocks
PCI DSS Requirements & Controls
PCI DSS Merchant Level Classification
The PCI DSS categorizes companies into four merchant levels based on the volume of transactions they process yearly.
The 4 Levels of PCI Compliance
- 6m+ transactions/year
- 1-6m+ transactions/year
- 20k-1m transactions/year
- <20k transactions/year
Choosing The Right PCI DSS SAQ
| SAQ Type | Description | Total Requirements | Total Controls |
|---|---|---|---|
| A |
Card-not-present merchants (e-commerce or mail/telephone-order) that completely outsource all account data functions to PCI DSS validated and compliant third parties. No electronic storage, processing, or transmission of account data on their systems or premises. Not applicable to face-to-face channels. Not applicable to service providers. |
7 | 27 |
| A-EP |
E-commerce merchants that partially outsource payment processing to PCI DSS validated and compliant third parties, and with a website(s) that does not itself receive account data, but which does affect the security of the payment transaction and/or the integrity of the page that accepts the customer’s account data. No electronic storage, processing, or transmission of account data on the merchant’s systems or premises. Applicable only to e-commerce channels. Not applicable to service providers. |
11 | 77 |
| B |
Merchants using only: • Imprint machines with no electronic account data storage, and/or • Standalone, dial-out terminals with no electronic account data storage. Not applicable to e-commerce channels. Not applicable to service providers. |
4 | 15 |
| B-IP |
Merchants using only standalone, PCI-listed approved PIN Transaction Security (PTS) point-of-interaction (POI) devices with an IP connection to the payment processor. No electronic account data storage. Not applicable to e-commerce channels. Not applicable to service providers. |
9 | 61 |
| C-VT |
Merchants that manually enter payment account data a single transaction at a time via a keyboard into a PCI DSS validated and compliant third-party virtual payment terminal solution, with an isolated computing device and a securely connected web browser. No electronic account data storage. Not applicable to e-commerce channels. Not applicable to service providers. |
6 | 34 |
| C |
Merchants with payment application systems connected to the Internet, no electronic account data storage. Not applicable to e-commerce channels. Not applicable to service providers. |
11 | 66 |
| P2PE |
Merchants using only a validated, PCI-listed Point-to-Point Encryption (P2PE) solution. No access to clear-text account data and no electronic account data storage. Not applicable to e-commerce channels. Not applicable to service providers. |
20 | 35 |
| SPoC |
Merchants using a commercial off-the-shelf mobile device with a secure card reader included on PCI SSC’s list of validated SPoC Solutions. No access to clear-text account data and no electronic account data storage. Not applicable to unattended card-present, mail-order/telephone order (MOTO), or e-commerce channels. Not applicable to e-commerce channels. Not applicable to service providers. |
19 | 111 |
| D |
SAQ D for Merchants: All merchants not included in descriptions for the above SAQ types. Not applicable to service providers. |
12 | 329 |
| D | SAQ D for Service Providers: All service providers defined by a payment brand as eligible to complete an SAQ. | 12 | 370 |
Get Started With Accorian
Accorian holds the prestigious distinction of having a team of highly Qualified PCI QSAs (Qualified Security Assessors) who specialize in assessing PCI compliance, with a particular emphasis on network infrastructure. In addition, we are CREST-accredited and an ASV (Approved Scan Vendor). These PCI accreditations underline our expertise and credibility in cybersecurity and PCI DSS compliance.
Furthermore, our potential client industry includes sectors such as banking, financial services, credit unions, eCommerce, and SaaS, all of which must adhere to payment card industry DSS requirements.
Accorian’s PCI DSS Experts
Penetration testing isn't just about finding vulnerabilities; it's about empowering organizations to fortify their defenses against evolving cyber threats. Through meticulous analysis and simulated attacks, we uncover weaknesses before malicious actors do, ensuring your digital assets remain resilient in the face of adversity.
Frequently Asked Questions (FAQs)
Q. What is PCI DSS and why is it important?
A. PCI DSS is a global security standard that protects payment cardholder data by enforcing strict security controls. It helps organizations avoid data breaches, fines, and reputational damage while ensuring customer trust.
Q. Who needs to comply with PCI DSS?
A. Any organization that stores, processes, or transmits credit card data—including merchants, service providers, and payment processors—must comply with PCI DSS.
Q. What services does Accorian provide for PCI DSS?
A. Accorian offers readiness assessments, gap analysis, remediation support, penetration testing, and audit preparation, guiding organizations through the entire PCI DSS certification journey.
Q. What are the benefits of becoming PCI DSS compliant?
A. Compliance reduces the risk of breaches, builds customer confidence, ensures alignment with industry standards, and avoids costly penalties from card brands or regulators.
Q. How does Accorian ensure a smooth PCI DSS compliance process?
A. Accorian combines its cybersecurity expertise with practical remediation guidance, mapping PCI requirements to business processes and providing clear roadmaps for successful certification.
Q. What are the 12 requirements of PCI DSS compliance?
A. PCI DSS is built around 12 core requirements grouped under domains like protecting cardholder data, maintaining secure systems, implementing access control, and testing networks. These include maintaining firewalls, using strong access controls, encrypting transmission of cardholder data, regularly testing security systems, and maintaining an information security policy, among others.