SOC 2
SOC 2 is no longer treated as a “once-a-year audit”
Accorian supports SOC 2 readiness and attestation through structured gap assessments and comprehensive control implementation. Powered by GORICO, our AI-enabled platform centralizes evidence management and enables continuous compliance.
Why Do You Need SOC 2?
SOC 2 is a cybersecurity compliance framework that evaluates how organizations protect customer data across the Trust Services Criteria. It demonstrates strong security controls and assures stakeholders that systems and data are effectively protected.
Importance of SOC 2
- Security Commitment & Continuous Improvement
- Meeting Client Expectations
- Bolstering Trust & Enhancing Security
- Accelerating Market Growth
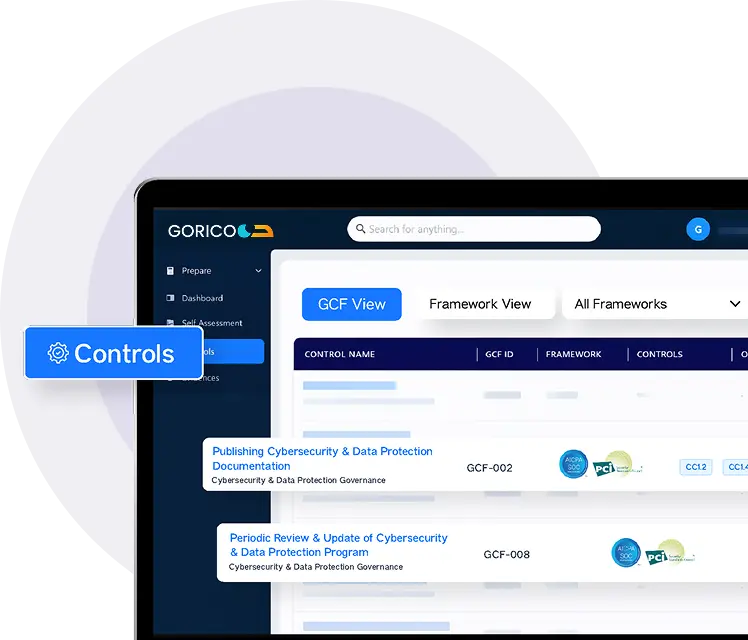
How GORICO Accelerates Your SOC 2 Journey
GORICO, with its AI-enabled capabilities, streamlines the SOC 2 process by centralizing control documentation, automating evidence collection, and enabling structured workflows across stakeholders while reducing manual effort, accelerating reporting, and strengthening overall control governance, making SOC 2 examinations more predictable and efficient.
Smarter GRC. Faster Outcomes.
FRAMEWORKS
Evidence Reusability
INTEGRATIONS
Hours SAVED
Trusted By Leading Clients
Accorian's expert team had seamlessly integrated as our dedicated security experts, serving as both our SOC 2 auditors and virtual CISO. The implementation of GORICO and its thorough risk assessments has significantly strengthened our security operations. What sets them apart is their genuine investment in our success, they’ve proven to be true strategic partners in our security mission.
– Trudy Janse van Rensburg
Types of SOC 2 Reports
Type I Report
01
Ideal for companies implementing security controls for the first time, the SOC 2 Type I report provides a point-in-time assessment without evaluating control maturity.
Type II Report
02
Ideal for organizations with established security controls, the SOC 2 Type II report evaluates control effectiveness and consistency over time, demonstrating ongoing security and compliance.
The Accorian Approach
- Define SOC 2 scope
- Initial self-assessment, interviews & evidence review
- Integrate your tech stack with GORICO to populate existing evidence seamlessly
- Identify security gaps and provide a prioritized remediation roadmap
- Query resolution
- Remediation / Control Designing Advisory
- Templates of audit artifacts.
- Evidence to be provided for remediated gaps by your team
- Our team will review remediated gaps and validate evidence through GORICO
- Type 1 Audit (Optional), is a point-in-time audit with an attestation report
- Perform final review of processes and controls for audit alignment
- Perform the SOC 2 Type 2 Audit and Attestation and write the SOC 2 Type 2 Audit Report.
- Validate control maturity through comprehensive testing and evidence verification
Who Should Get SOC 2?
SOC 2 reports are often required for service firms across industries that store, process, or transfer sensitive data for their clients. We combine SOC 2 with frameworks like ISO/IEC 27001, ISO/IEC 27002, HITRUST, and HIPAA to streamline audits and reduce audit fatigue. We serve a diverse portfolio of industries, including:
Technology and Cloud Computing Entities
Virtual Currency Service Providers
Managed IT Service Providers
Data Centers
SaaS Providers
Web-Hosting Service Providers
Processors of Payrolls and Medical Claims
Accorian’s SOC 2 Experts
Accorian’s SOC 2 services are effective in enhancing the security, availability, confidentiality and privacy requirements of organizations. We evaluate your systems for compliance, locate security weaknesses and suggest measures to address those weaknesses – all for the purpose of ensuring data protection and building confidence with client’s expectations.
Get Started With Accorian
Accorian is a leading cybersecurity and compliance firm specializing in SOC 2 readiness and reporting. Our auditors, leveraging deep technical expertise and supported by structured workflows within GORICO, conduct comprehensive assessments, perform gap analyses, and implement required controls for Type I and Type II engagements. By strengthening privacy and security measures, we enhance your market credibility and deliver a sustained competitive advantage.
Frequently Asked Questions (FAQs)
Q. What is SOC 2 and why is it important?
A. SOC 2 is an attestation standard that evaluates how well an organization secures client data across trust principles like security, availability, and confidentiality. It builds credibility, reduces risk, and is often required by customers in regulated industries.
Q. What is the difference between SOC 2 Type 1 and Type 2?
A. Type 1 reports evaluate controls at a specific point in time, while Type 2 reports assess controls over an extended period, demonstrating consistent effectiveness.
Q. How does Accorian simplify SOC 2 compliance?
Q. Which industries benefit most from SOC 2?
Q. How long does it take to achieve SOC 2 attestation?
A. Timelines vary by readiness, but with Accorian’s structured approach and automation, organizations can complete the SOC 2 process significantly faster than traditional methods.
Q. What is the difference between SOC 1 and SOC 2?
A. SOC 1 audits internal controls over financial reporting (ICFR), relevant to service providers affecting clients’ financials. SOC 2 evaluates controls around data security, availability, integrity, confidentiality, and privacy – relevant to technology and SaaS providers managing client data.
Q. Is SOC 2 the same as ISO 27001?
A. No – they overlap but serve different purposes. SOC 2 is an audit attestation report verifying control effectiveness, whereas ISO 27001 is a certifiable standard for building a management system (ISMS). Many organizations use them together to satisfy both audit and systemic requirements.