Risk Assessment
Gain clear visibility into company risks with a structured, risk-based approach.
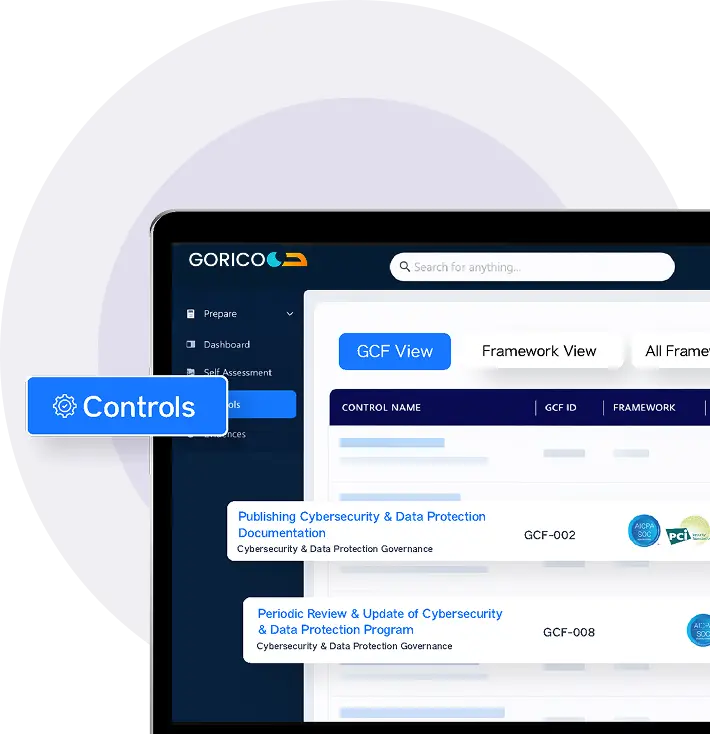
Our experts systematically identify and classify overall company risk based on criticality, assess inherent and residual risks, and provide actionable insights to strengthen third-party risk management. Powered by GORICO, our AI-enabled platform, we streamline overall company risk workflows, centralize risk intelligence, and deliver continuous visibility.
Why Do You Need Risk Assessment?
A Risk Assessment is a structured process used to identify, analyze, and prioritize potential risks that could impact an organization’s operations, data, systems, or reputation.
Importance of Risk Assessment
- Identify vulnerabilities early
- Prioritize what matters most
- Strengthen security posture
- Manage third-party & overall company risks
- Meet compliance requirements
- Enable informed decision-making
How GORICO Accelerates Your Risk Assessment Journey
GORICO, with its AI-enabled capabilities, streamlines the Risk Assessment process by centralizing control documentation, automating evidence collection, and enabling structured workflows across stakeholders while reducing manual effort, accelerating reporting, and strengthening overall control governance, making Risk Assessment examinations more predictable and efficient.
Smarter GRC. Faster Outcomes.
FRAMEWORKS
Evidence Reusability
INTEGRATIONS
Hours SAVED
Types of Risk Assessment
01
Enterprise Risk Assessment
It identifies and evaluates financial, operational, strategic, and compliance risks across the organization.
02
HIPAA Risk Assessment
Designed for healthcare organizations, it risks to PHI confidentiality, integrity, and availability while ensuring HIPAA compliance and protection of sensitive data.
03
NIST 800-30 Risk Assessment
Aligned with the NIST framework, it identifies, analyzes, and manages information system risks to support structured cybersecurity risk management and compliance.
04
Questionnaire-Based Risk Assessment
Uses structured questionnaires to identify weaknesses across processes, technologies, and controls.
05
Vendor Risk Assessment
Assesses risks associated with third-party vendors, ensuring they meet security and compliance standards to protect the organization’s security posture.
Elements of Risk Management
The Accorian Approach
Risk assessments can span the entire organization or focus on specific systems and components, incorporating vulnerability analysis to quantify threats. Regular, incremental assessments ensure comprehensive coverage, supporting defense, compliance, continuity, cost savings, and protection of assets and trust amid evolving security needs.
Identifies and evaluates risks to IT systems and data, including malware, breaches, and system failures, by assessing their likelihood and impact. Implements controls, training, response plans, and monitoring to manage risks while ensuring security, compliance, and business continuity.
Risk treatment entails addressing recognized risks and vulnerabilities through acceptance, mitigation, or avoidance. Acceptance refers to retaining a known risk within the organization's tolerance; mitigation minimizes risks through security measures and training; and avoidance eliminates actions that provide unacceptable risks.
Get Started With Accorian
Accorian delivers a comprehensive suite of security risk assessments aligned with leading frameworks, including HITRUST, PCI DSS, HIPAA, ISO 27001, and more. Our proven, structured methodology enables organizations to efficiently identify and evaluate risks through an extensive, interconnected library of asset types, threats, vulnerabilities, and risk scenarios. By leveraging this intelligence-driven approach, clients accelerate assessment timelines, gain deeper risk visibility, and achieve faster, more reliable outcomes without the burden of starting from scratch or navigating complex requirements without expert guidance.
Accorian's Risk Assessment Experts provide unparalleled depth in their expertise on risk identification and analysis across people, process, and technology. Knowledge of industry standards such as ISO 27001, SOC 2, HIPAA, PCI DSS, and others ensures well-tailored assessments that truly enhance your organization's security posture. Through actionable insights, we power businesses to address vulnerabilities proactively, ensure compliance, align risks with organizational goals and thereby enhance resilience within an always-evolving threat landscape.
New At
Accorian
New At Accorian
Frequently Asked Questions (FAQs)
Q. What is a cybersecurity risk assessment?
A. A risk assessment identifies and evaluates potential threats to your information assets, helping you understand exposure, likelihood, and impact before an incident occurs.
Q. Why are risk assessments important?
A. They allow organizations to prioritize mitigation efforts, comply with frameworks like ISO, SOC, and NIST, and make informed security investments.
Q. What is Accorian’s approach to risk assessment?
Q. How often should organizations conduct risk assessments?
A. At least annually or after major operational, technological, or regulatory changes to ensure controls remain effective.
Q. What are the deliverables of a risk assessment?
A. A detailed risk register, threat-impact matrix, prioritized mitigation roadmap, and executive summary for leadership decision-making.