Executive Summary
The Cyber Resilience Act (CRA) introduces a unified set of mandatory cybersecurity requirements for digital products across the EU, addressing long-standing gaps in product security and inconsistent update practices. It places clear responsibility on manufacturers to build security into products from the outset and maintain it throughout the lifecycle.
With phased enforcement starting in 2024 and full compliance by 2027, organizations must shift from treating security as a best practice to a legal obligation. Early preparation will be key to managing risk, avoiding penalties, and building trust in an increasingly security-focused market.
Why the EU Cyber Resilience Act Is a Game Changer
Digital products, whether they are smart home devices or enterprise software, have become deeply embedded in how we live and work. But there’s a problem: many of these products hit the market with weak security and inconsistent update practices, leaving them exposed to cyber threats. In today’s interconnected world, one vulnerable product doesn’t just affect a single user, it can ripple across entire organizations or even supply chains.
Until recently, cybersecurity rules across the EU were scattered and inconsistent. This made things confusing for manufacturers and gave users little clarity on which products were actually secure. That’s where the Cyber Resilience Act (CRA) steps in. It introduces a standardized set of mandatory cybersecurity requirements for digital products across the EU. More importantly, it shifts accountability to manufacturers, requiring them to take ownership of security from start to finish.
With cyber threats becoming more sophisticated, the CRA is a significant move toward building safer and more reliable digital ecosystems.
Decoding the Cyber Resilience Act (CRA)
At its core, the CRA is an EU regulation designed to ensure that digital products, software, applications, and connected devices, are secure throughout their lifecycle. This includes everything from smartphones and laptops to IoT devices, operating systems, mobile apps, and firmware.
The key idea is simple: security shouldn’t be an afterthought.
Manufacturers are expected to build products securely from the beginning and continue addressing vulnerabilities through regular updates.
Why was this needed?
- Many products today are released with poor security controls.
- Updates are often irregular or missing altogether.
- Users don’t have enough information to judge whether a product is secure.
The CRA aims to fix these issues by setting clear expectations and responsibilities.
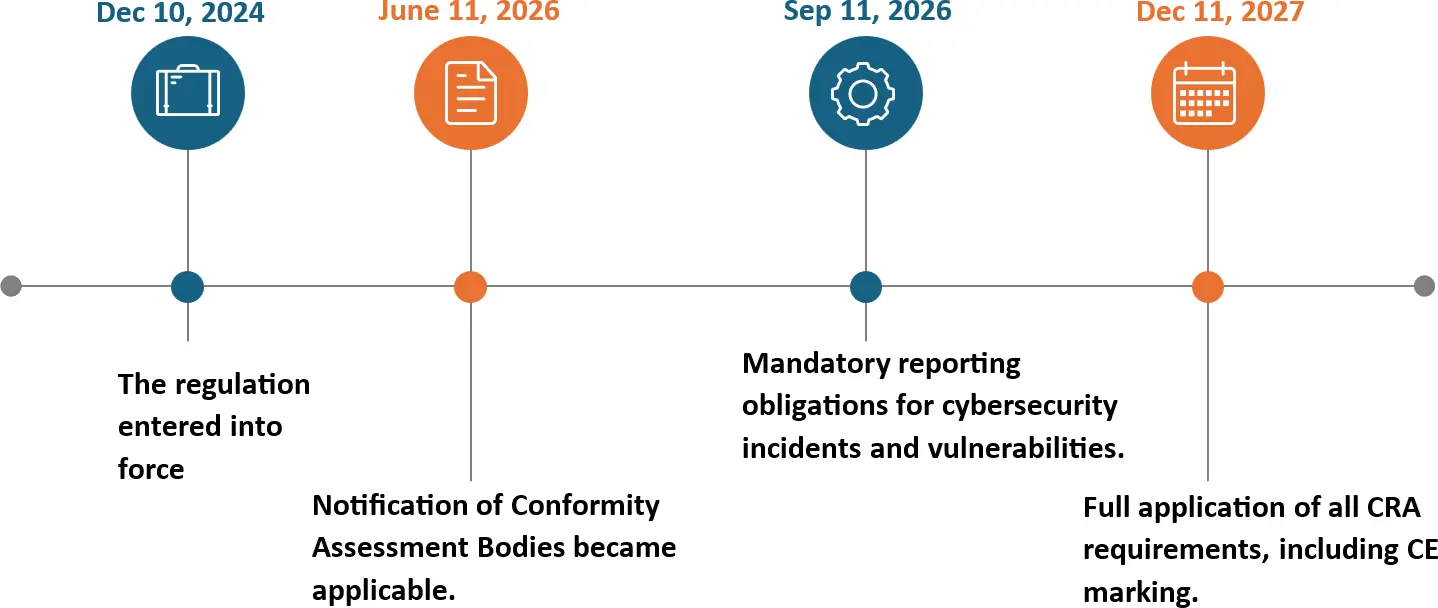
Timelines You Should Know
The CRA isn’t being enforced overnight, it’s being rolled out in phases to give organizations time to prepare.
- December 2024 – Regulation comes into effect.
- September 2026 – Mandatory vulnerability and incident reporting begins.
- December 2027 – Full compliance required across all requirements
This phased approach gives organizations breathing room—but waiting too long to prepare could create last-minute pressure.
CRA Scope: What’s Covered (and What’s Not)
The CRA applies to most digital products that can connect to a network or another device.
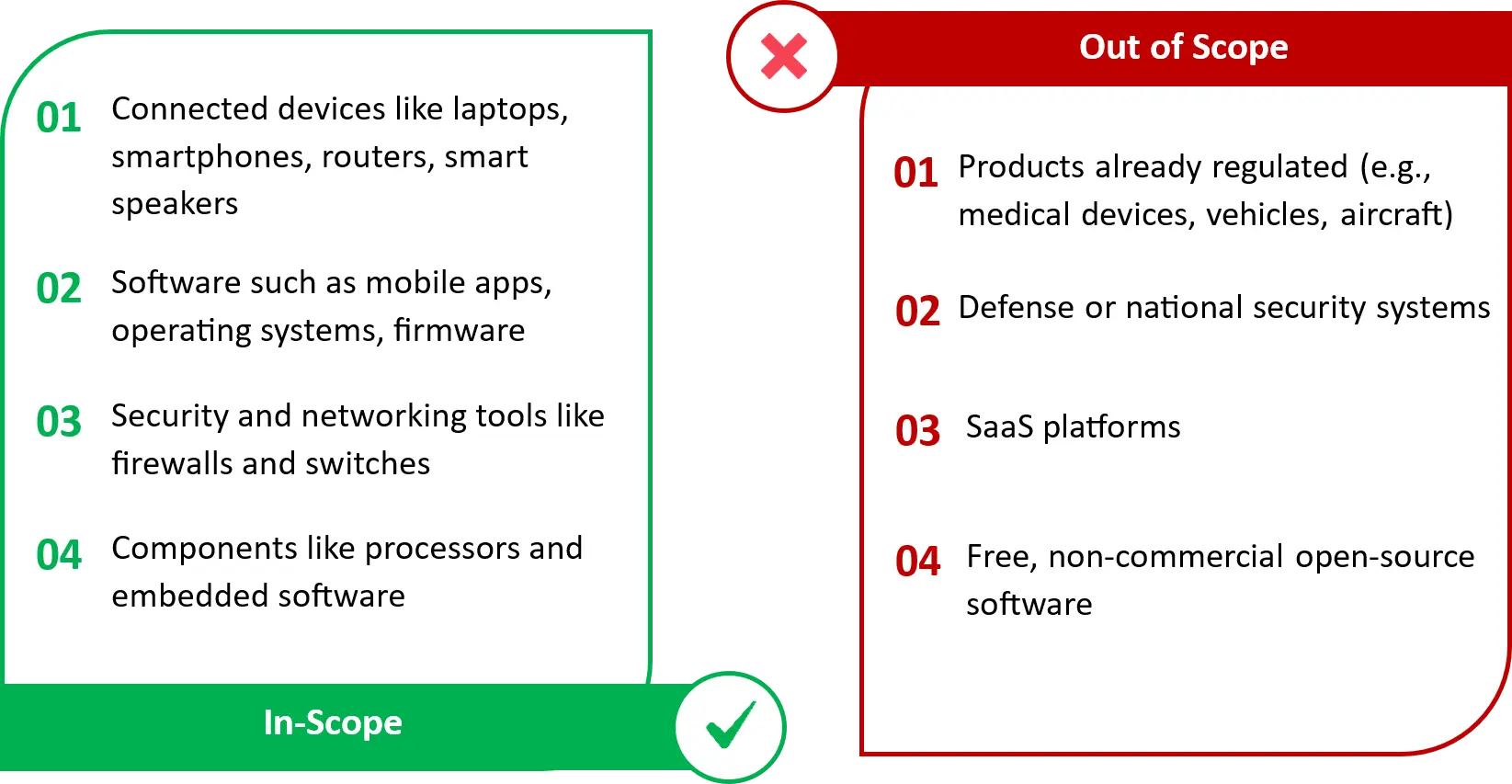
These exclusions exist to avoid overlapping with other regulations or because different rules already apply.
What Happens If You Don’t Comply
Non-compliance isn’t just a technical issue it can have serious business consequences:
- Fines up to €15 million or 2.5% of global annual turnover (whichever is higher)
- Products being removed or restricted in the EU market.
- Mandatory recalls or corrective actions
Key Requirements
The CRA introduces practical, product lifecycle-based security expectations which organizations must implement:
| Requirement | What it Means | What Organizations Must Do |
|---|---|---|
| Security by Design & Default | Build products securely from the start | Use secure configurations, avoid default passwords, minimize risks during design |
| Vulnerability Management | Find and fix security issues continuously | Monitor vulnerabilities and release timely patches/updates |
| Incident Detection & Reporting | Identify and respond to cyber incidents | Detect incidents quickly and report major issues within required timelines |
| Security Updates | Keep products secure over time | Provide regular updates and support throughout the product lifecycle |
| SBOM (Software Bill of Materials) | Know what’s inside your product | Maintain a list of all software components to track risks |
| Technical Documentation | Prove compliance | Maintain records showing how security requirements are met |
Who Is Responsible for CRA Compliance?
Compliance isn’t limited to one team; it spans the entire product supply chain.
Manufacturers: Own the product’s security end-to-end, including design, updates, and vulnerability management. This includes conducting conformity assessments, maintaining technical documentation, providing security updates, and managing vulnerabilities throughout the product lifecycle.
Importers: Ensure products entering the EU meet CRA requirements and have proper documentation.
Distributors: Verify compliance before making products available in the market.
Integrators / Retailers: Ensure only compliant products reach customers and support corrective actions if needed
A Major Shift: From “Good Practice” to Legal Requirement
Previously, product security was often treated as the best practice, something nice to have but not always enforced.
The CRA changes completely. Security is now mandatory by law. Manufacturers are legally responsible for ensuring their products are secure not just at launch, but throughout their lifecycle.
- Ad-hoc security practices → Structured, repeatable processes
- One-time checks → Continuous monitoring and updates
- Shared responsibility → Clear, enforceable accountability
Product Categories Under CRA
| Category | Risk Level | Description | Examples | Assessment Requirement |
|---|---|---|---|---|
| Default | Low | Products with basic functionality and limited cybersecurity impact. | Smart home devices, printers, Bluetooth speakers, media apps | Self-assessment |
| Important – Class I | Medium | Products that support security functions or are widely used across systems. | Password managers, VPNs, operating systems, and routers | Self-assessment allowed if recognized standards or certifications are used; otherwise, external assessment |
| Important – Class II | High | Products that manage or secure systems and networks. | Firewalls, intrusion detection systems, hypervisors | Mandatory third-party assessment |
| Critical | Very High | Products used in sensitive or critical environments. | Smart meter gateways, smart cards, cryptographic devices | Formal certification required |
The Cyber Resilience Act classifies products based on their cybersecurity risk and impact. This classification determines the level of assessment required before a product can be placed on the EU market.
Additional Note on Important – Class I
For Important Class I products, organizations can perform self-assessment only if they follow recognized compliance approaches, such as:
a. Harmonized Standards: Predefined security standards aligned with EU requirements
b. Common Specifications: Detailed rules provided when standards are not available
c. Certification Schemes: Formal frameworks to validate product security
If none of these are applied, the product must go through an external third-party assessment.
Preparing for CRA Compliance
The CRA requires organizations to think about security across the entire product lifecycle. This isn’t just a security team problem, it involves engineering, governance, and operations. With reporting obligations starting in 2026 and full compliance required by 2027, early preparation can make a huge difference.
Accorian supports organizations in building a structured and practical path to CRA compliance through the following key areas:
a. Scoping & Product Classification
Identify which products are in scope and categorize them by risk
b. Gap Assessment
Evaluate current practices against CRA requirements
c. Conformity Assessment
Decide whether self-assessment or third-party validation is needed
d. Vulnerability and Incident Reporting Readiness
Build processes to meet strict reporting timelines
e. Supply Chain and Third-Party Risk Management
Strengthening oversight of third-party components and vendors
Common Questions Around CRA
Q. What counts as a product with digital elements?
A. Any hardware or software that can connect to a device or network, directly or indirectly.
Q. Do products developed before CRA enforcement need to comply?
A. Products released before full enforcement (Dec 2027) may not need full compliance, but reporting obligations can still apply.
Q. What are the reporting obligations for vulnerabilities?
A. Manufacturers must report actively exploited vulnerabilities once they become aware of them within 24 hours. This includes vulnerabilities in their own products and integrated third-party components.
Q. Who handles third-party vulnerabilities?
A. Component providers fix the issue, but product manufacturers must manage the risk and inform users.
Q. What is a conformity assessment?
A. It’s the process of verifying that a product meets CRA requirements—either through self-assessment or third-party validation.